Career 15 Vacancies 250+ Employees
Career 15 Vacancies 250+ Employees
InfoGuard AG (Headquarter)
Lindenstrasse 10
6340 Baar
Switzerland
InfoGuard AG
Stauffacherstrasse 141
3014 Bern
Switzerland
InfoGuard Deutschland GmbH
Landsberger Straße 302
80687 Munich
Germany
Dynamite Phishing ‒ Emotet can forge e-mails almost perfectly

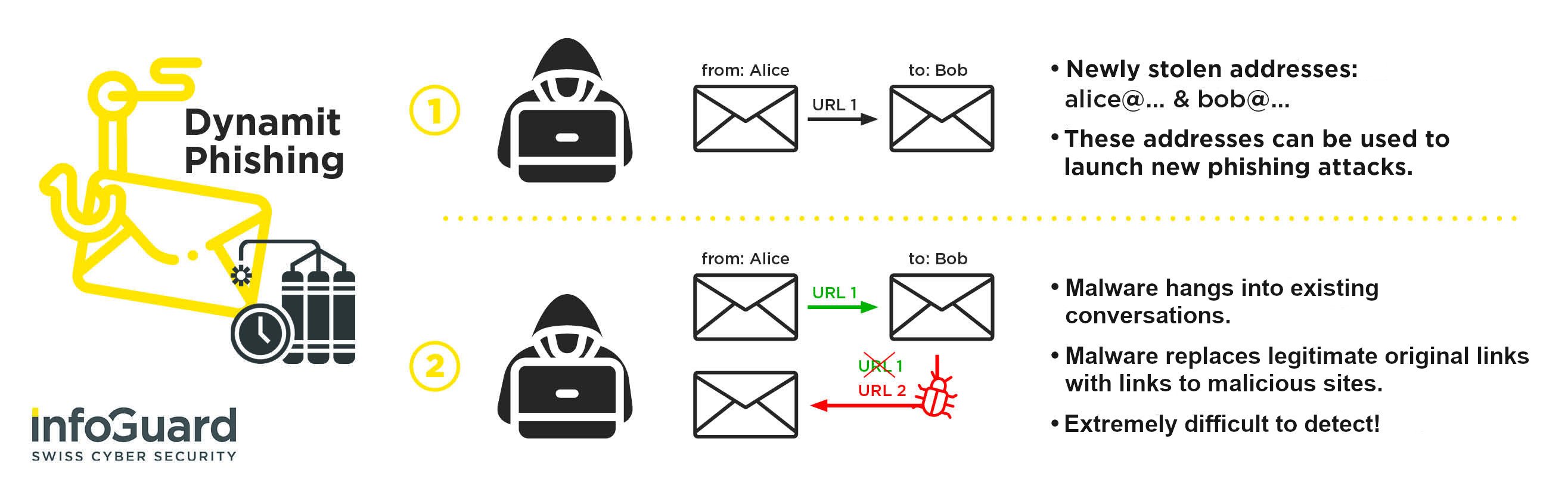
Since autumn 2018, the malware «Emotet» has been collecting stored Outlook e-mails on every infected system. Until now, these mails were only used to steal alleged sender and recipient addresses for further phishing e-mails. But now Emotet is using the actual content of the stolen e-mails to refine its strategy and attacks even further. Using the e-mails that were hacked earlier, the cyber criminals create amazingly genuine «dynamite phishing e-mails». What does that mean for you?
Imagine that you are actively exchanging e-mails with a person you know and you are expecting a download link for a document. After a long wait, the e-mail finally arrives and without hesitation, you click on the link. But what you don't know at that moment is that a virus has infiltrated your conversation and what is supposed to be a link to the document is actually downloading another virus ...
Emotet and Outlook Mail Harvesting
In October 2018, security researchers around the globe found a new module in what is currently the most common and most dangerous malware, Emotet. This module, known as the «E-Mail Harvester», collects all the e-mail conversations on an infected system and sends them in encrypted form to the C2 (Command & Control) server (Figure 1). At the time, there were suspicions that the e-mails were not being stolen solely for the purposes of espionage, but that the attackers had far more dangerous plans. So it was no surprise to our analysts when last week, the CERT announced that Emotet was using the stolen e-mail conversations to propagate itself even further.
So how does dynamite phishing work? Well, specific conversations are selected that contain links to documents (for example to online storage such as Dropbox) and where there has already been a lot of e-mail traffic. The e-mail content and even the link text are mostly ignored by the virus. However, the link itself is replaced, and it leads to an infected Word document, which downloads the Emotet when macros are activated, then installs it on the system (Figure 2). In some cases, it has also been noted that shortly before the link a text, such as «The important documents can be found under the following link» was inserted. Another variant is that the infected document is attached directly to the e-mail.
What makes Emotet so dangerous?
In security awareness trainings, we are always explaining that the most important thing in social engineering and phishing attacks is the so-called «story». The attacker studies his or her victim and creates a story. By doing so, (s)he is seeking to tempt the victim into carrying out actions that he or she would not normally do. For example, the story of the craftsman who is supposed to carry out work and as a result gains access to sensitive business areas (social engineering), or the story of the CEO, who writes an e-mail to the employee and instructs him to make a financial transaction (CEO Fraud / Whaling).
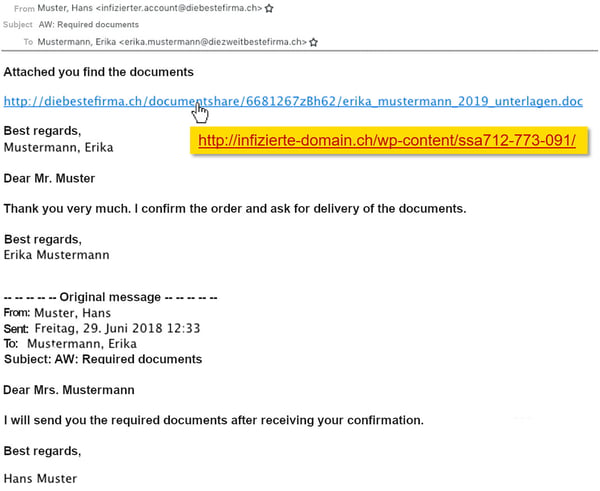
The new Emotet module then finesses the story; because the attacker does not need to invent a story; instead he or she can directly link into a real story that already exists. In the Security Awareness training sessions with our clients, we are always preaching, «never open any unexpected attachments!»
So protect yourself against dynamite phishing and Emotet!
So now you know how Malware Emotet and Dynamite Phishing work in general and what makes them so dangerous; but how do you go about protecting yourself against that?
- Rely on Security Awareness Trainings
Training your employees is a sensible measure to implement and is relatively simple. However, you should make clear to them beforehand that caution is recommended when attaching files to e-mails. Emotet works with Office documents, which are often assumed to be invoices in Microsoft Word .doc format. If in doubt, the proven strategy is to briefly ask the alleged sender whether the e-mail actually originated from him or her. This takes no time at all and can prevent a great deal of trouble. Also, make it clear to your employees that there is no shame in not immediately exposing a phishing e-mail and asking the recipient - quite the opposite! - Deactivate macros
The actual virus infection does not normally take place at the time when the document is opened; it requires macros to be run. These are command chains such as automating layout tasks or performing calculations in tables. Instead, Emotet developers use the commands to download and install malware from the Internet. In Microsoft Office, macros are disabled by default, but they can easily be enabled by clicking on «Enable content». And of course the malware developers use any tricks they can to get the user to activate the macro. What a lot of people don't know is that normally you don't need macros for a document that is sent by e-mail. If a file requires a macro to be activated, it often means it is a Trojan. If you can, you should deactivate this dangerous function!
Security Awareness training sessions by experts
In our experience, security awareness training is one of the most effective methods of raising employee awareness. Notable examples are presented, and the specific dangers lying in wait for the company are dealt with.
In our next blog article, you'll learn more about whaling and what to do when a phishing attack is successful. Subscribe to our blog updates now and make sure you never miss another article!
Blog

Zero Trust Maturity Model 2.0: Reifegradmodell auf 5 strategischen Säulen

SWIFT CSCF v2025 erhöht den Druck: Nur cyberresilient ist compliant


